Real engagements.
Named clients. Measured outcomes.
We show only the work we can name, with the metrics our clients have verified. No aspirational blurs, no stock mock-ups — just the engagements we've already delivered, with written permission from each partner to share.
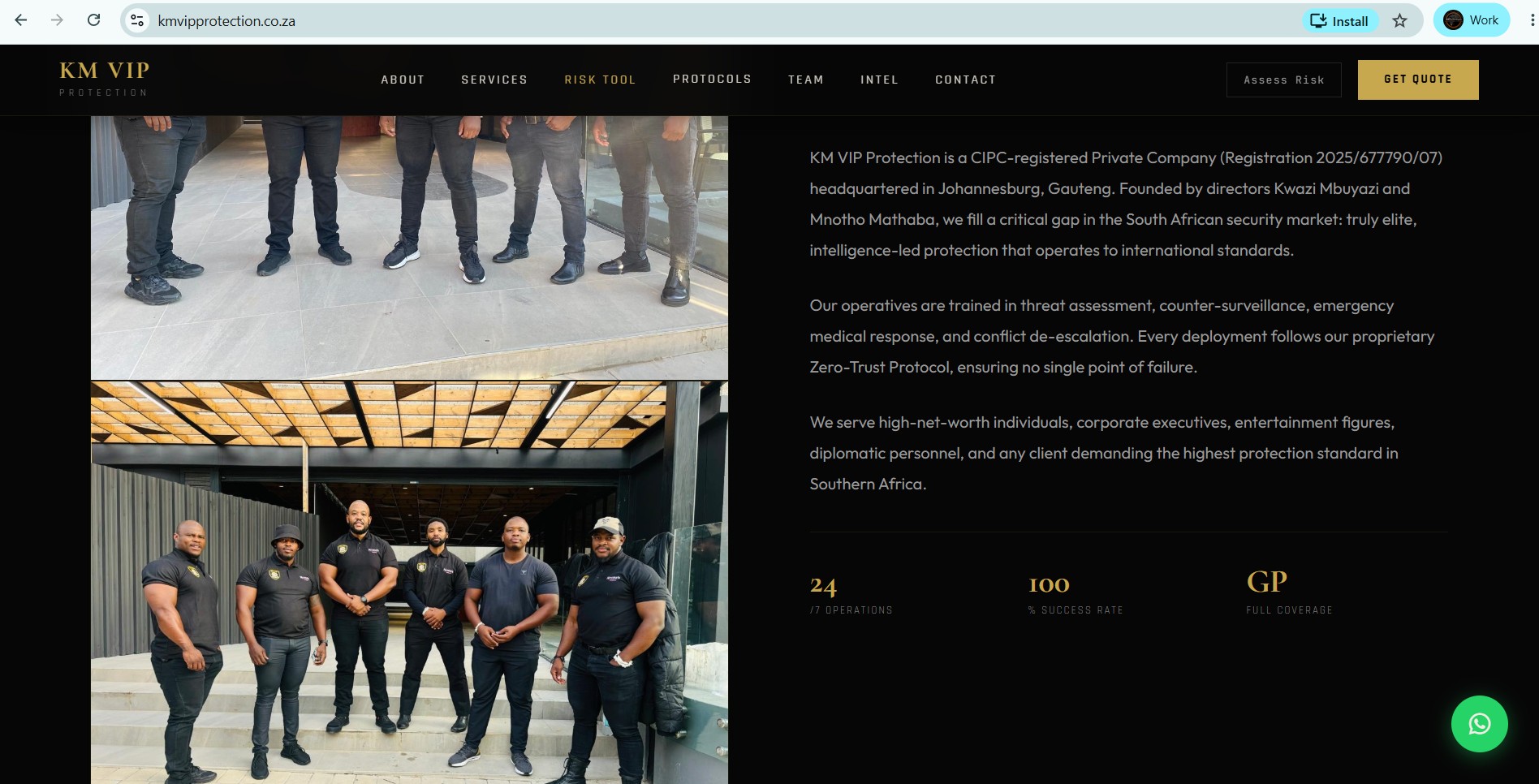
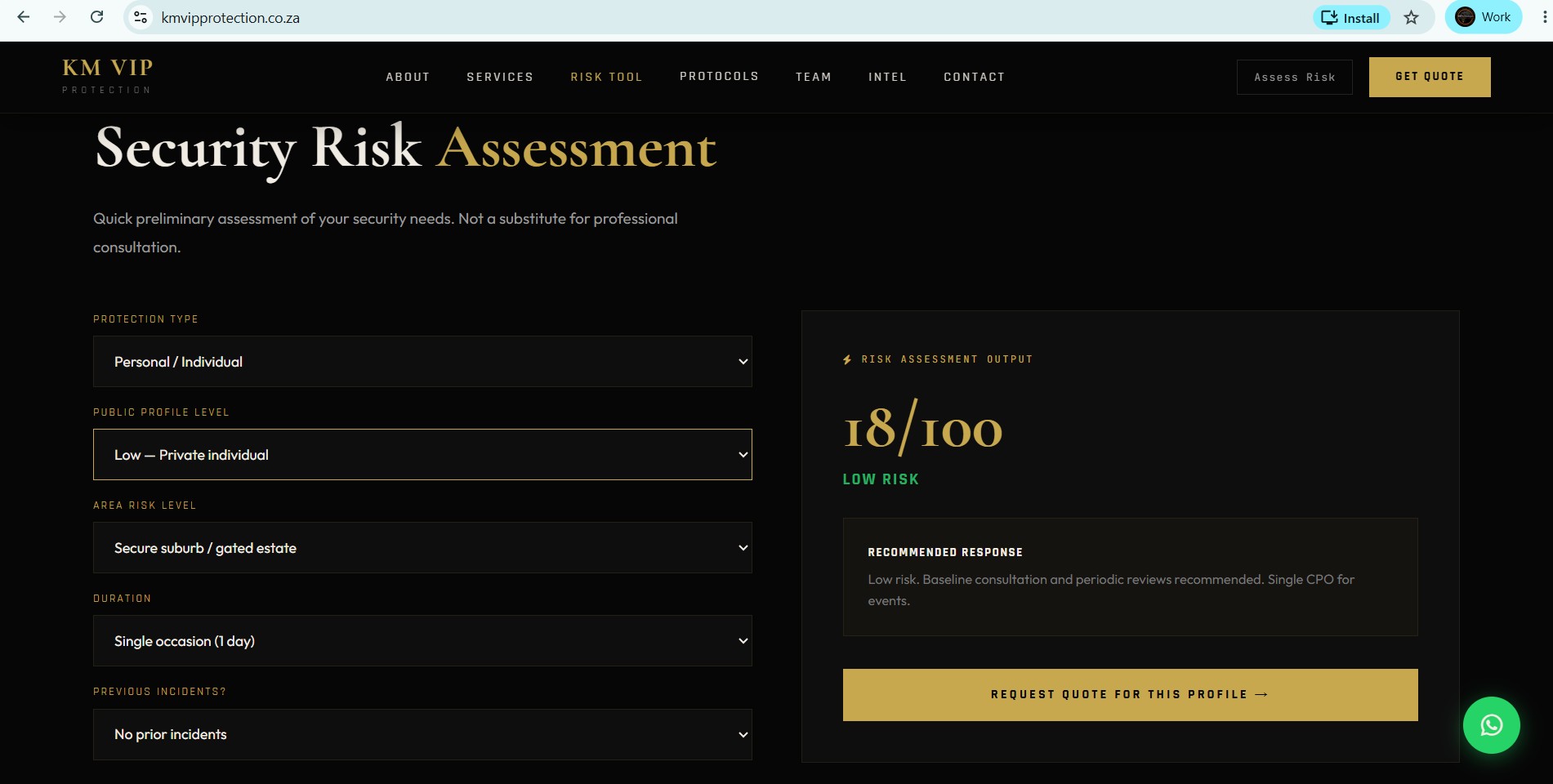
KM VIP Protection — PSIRA-Registered
Complete digital asset pack for a PSIRA-registered private security firm. Anti-template website built from ground up, full social media channel integration, and digital ownership transfer. Permanent business asset, not a rental.
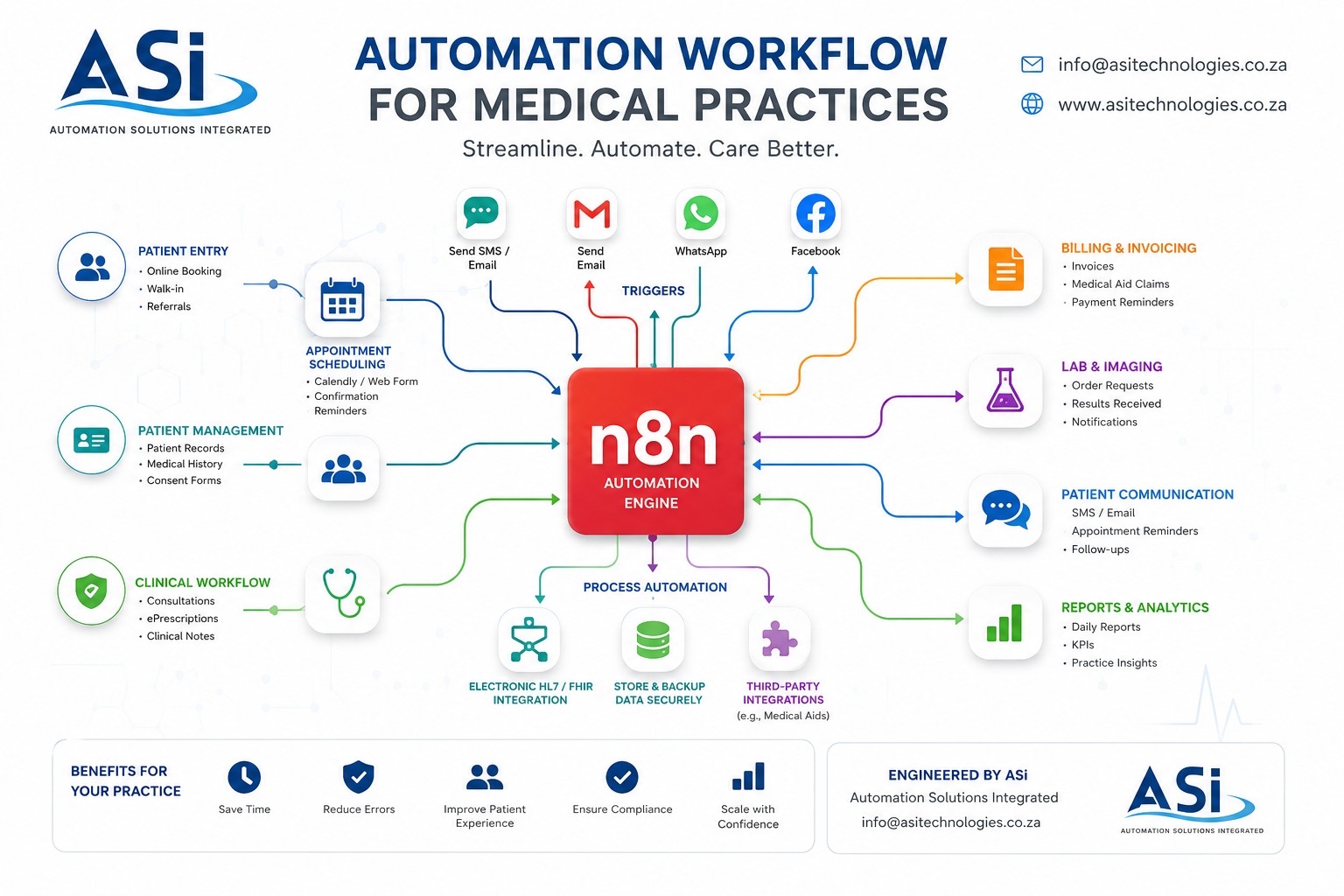
Dr. Tonda Mabasa Medical Practice
Not a traditional website, but an engineering-grade Clinical Mainframe. Engineered to support WebRTC-enabled Telehealth virtual consultations, diagnostic integrations, and sovereign patient data control. An investment into permanent practice infrastructure, not a rented platform.
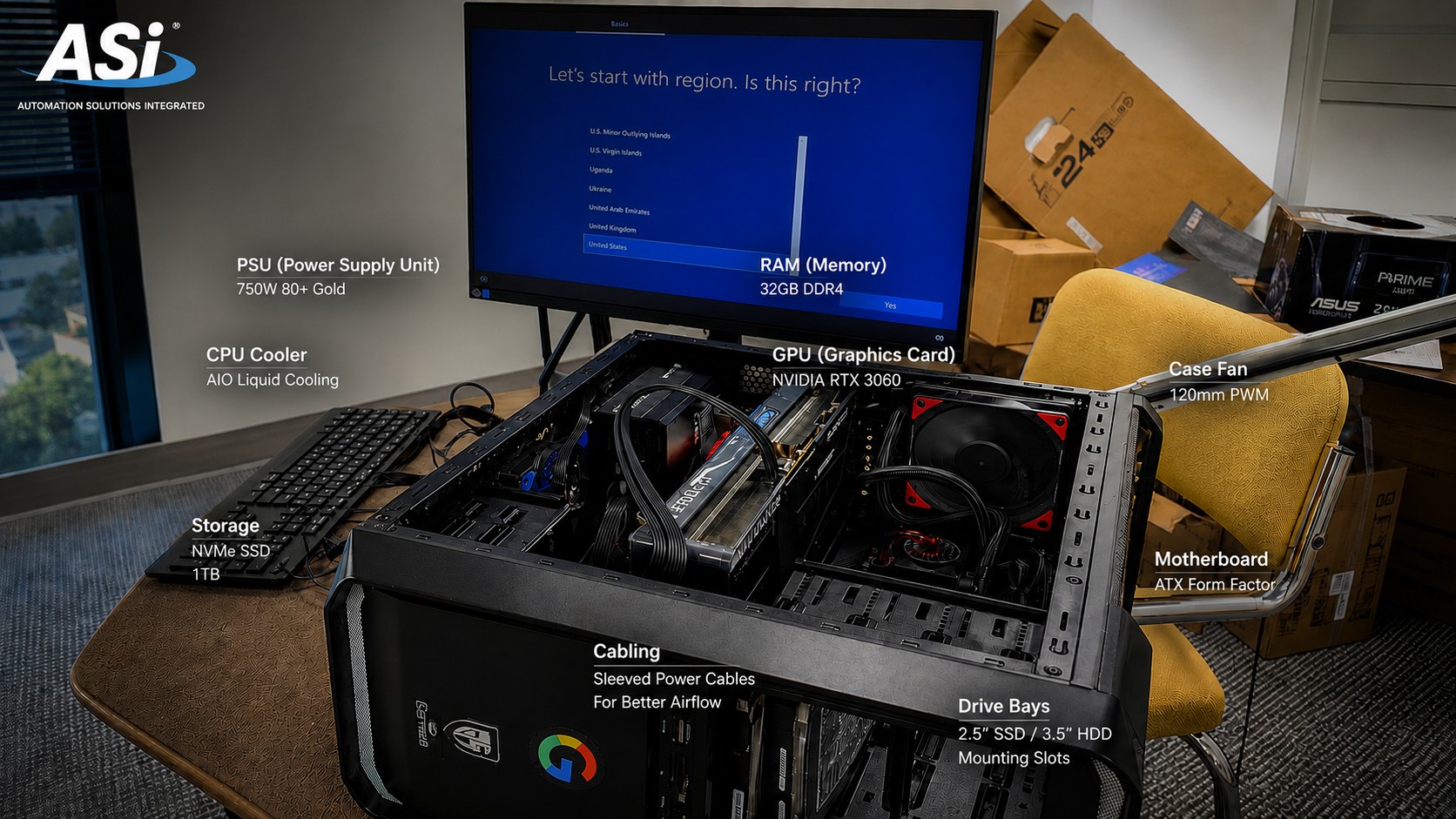
MobiDokta Tech Repairs
High-efficiency service platform for an independent IT repairs company focusing on deep hardware and software remediation. Built with rapid booking flows and trust-building technical showcases.
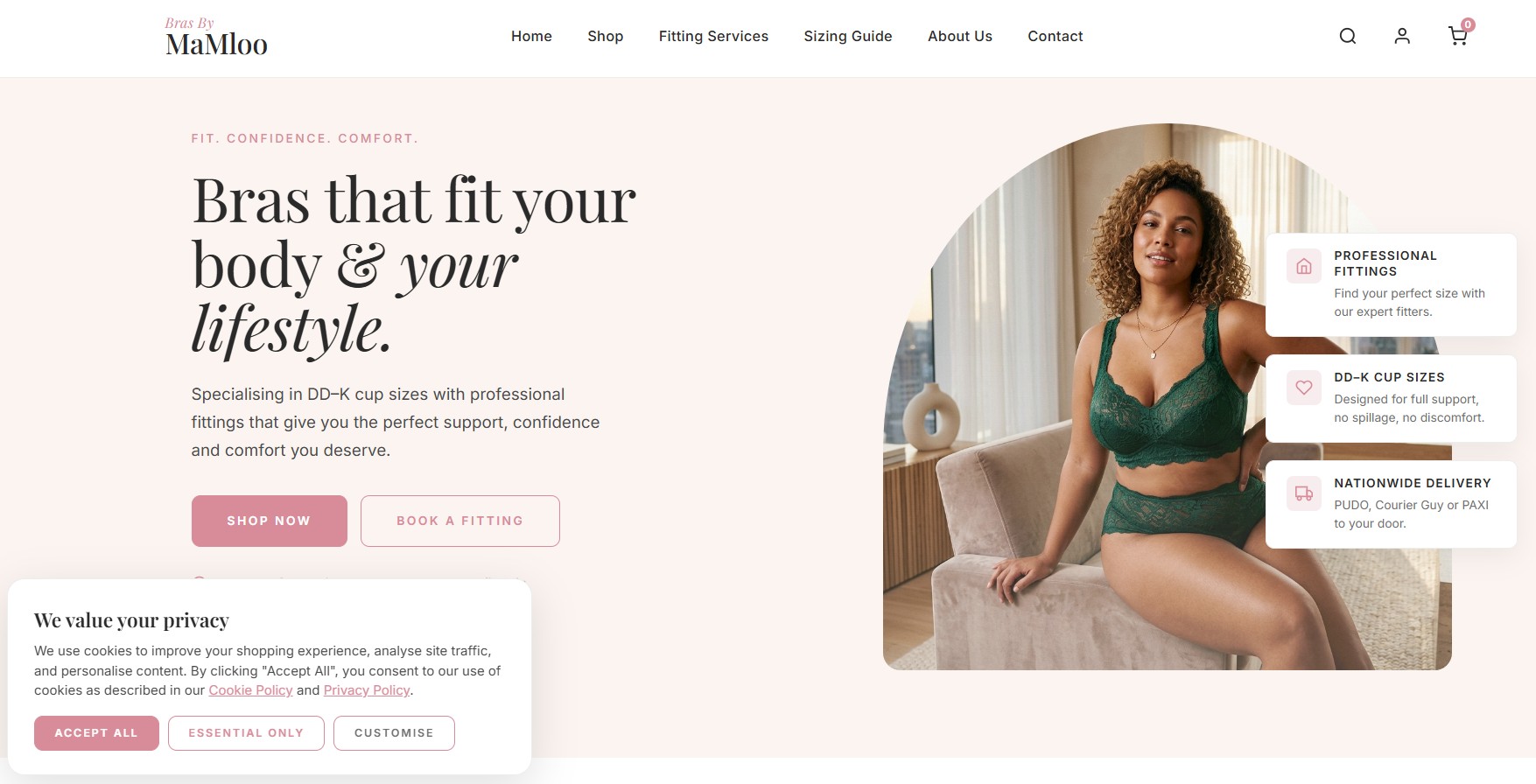
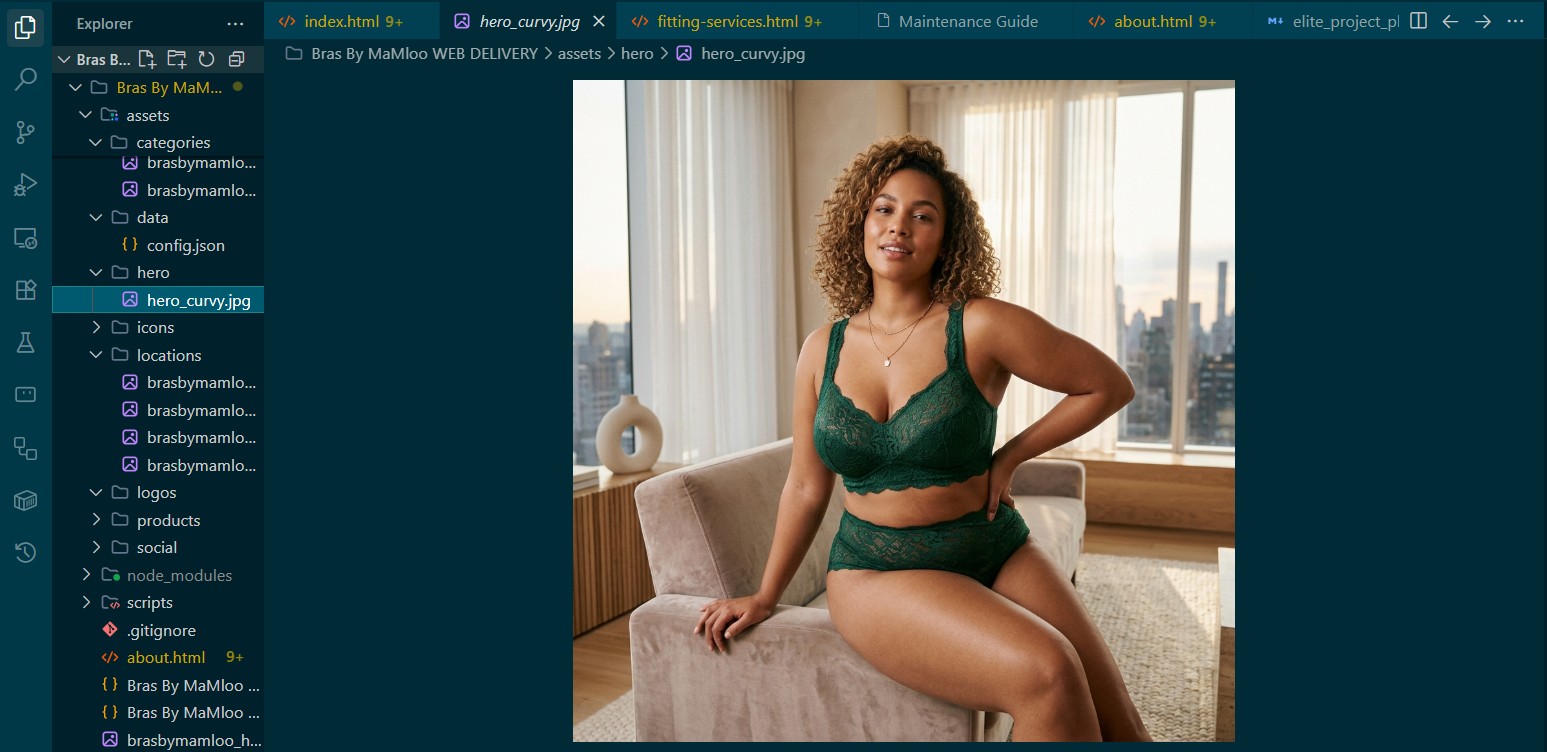
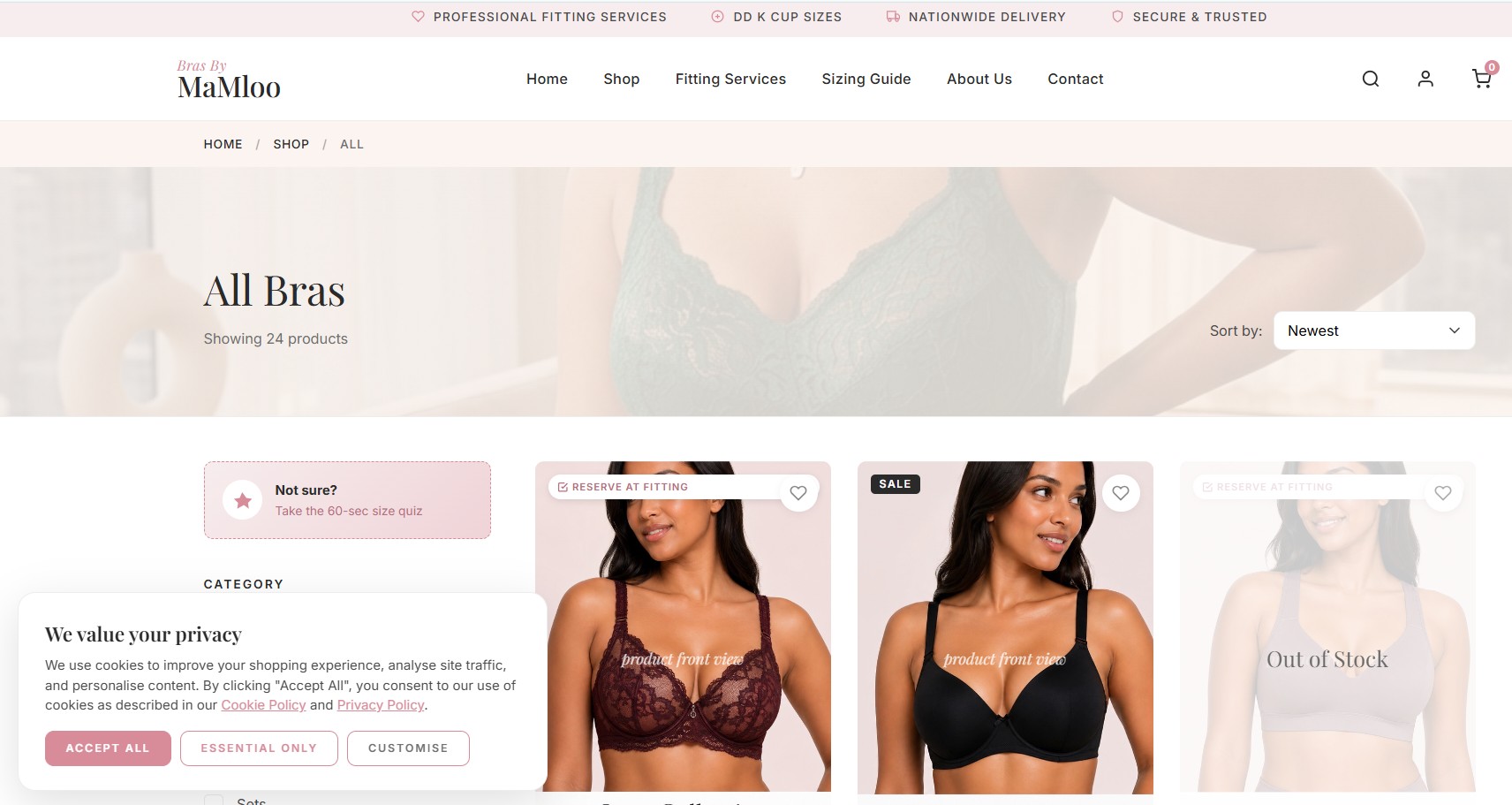
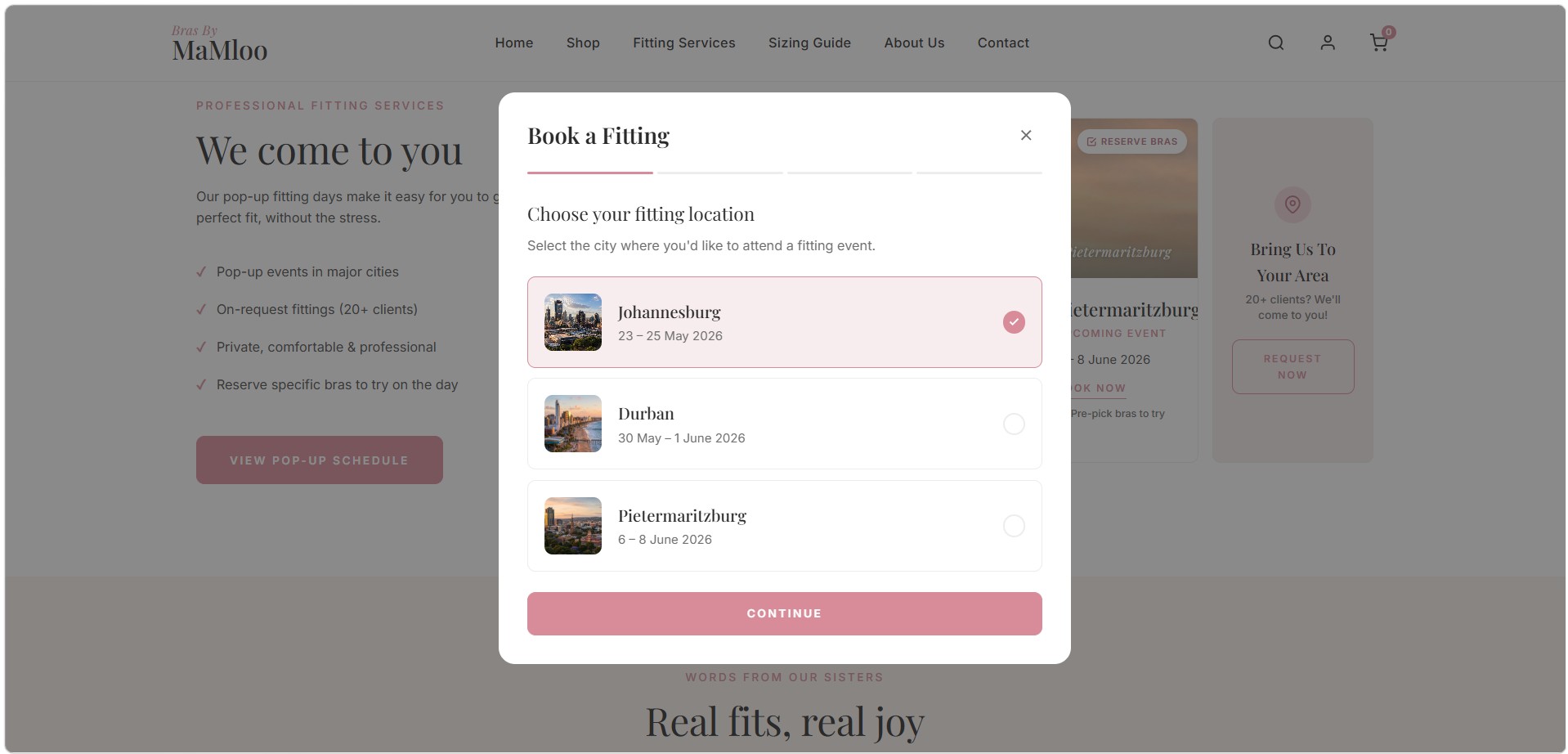
Bras By MaMloo
High-conversion e-commerce platform specializing in DD-K cup sizes. Features a frictionless WhatsApp checkout, dynamic product filtering, and an integrated booking system for professional fitting services.